In this day, social media is everywhere. Checking trendy outfits on Instagram, retweeting cat videos on Twitter, or going to watch some fun tutorials on YouTube. It's impossible to not have social media.
But with all the fun, the importance of strong passwords is often overlooked. In a social experiment done by Kaspersky Lab, a cybersecurity firm, people were very quick to say the recipe used to cook up their passwords consisted of the following:
- Significant others name or year dated
- Names of: pet, grandma, mom name
- Sports team names or team players names
- Places visited
The main problem with the password quality the above data would generate is the password would be made up of dictionary words, meaning easy to understand words found in a dictionary. Examples of passwords would be TommylovesJess2018, IloveRocko1234, and Gmama1954.
The main reason people use simple dictionary-based passwords is that they rely on human memory to remember their passwords.
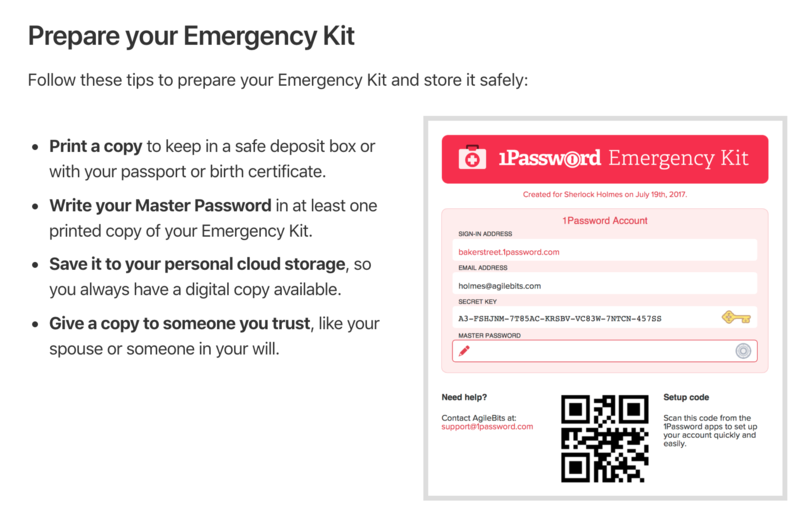
It is much easier to remember Ilovecats1234 than QdZKSKU5cH~<B[An. However, in this day and age, it's time to make technology work in your favor. Using a password manager you can create complex passwords for each of your logins and never worry about having to remember them. In the following write up, we will examine some of the most used password managers and some of the cybersecurity attacks used to guess passwords.
Let's Talk About Account Takeovers
An account takeover is when an attacker has gained access to your personal account on a site or app. For the purpose of this tutorial, let's assume the takeover is due to someone knowing your login credentials. As the saying goes: "Why hack it when you can just login." There is a couple of ways someone can obtain your credentials some are:
- Data Dump, a massive list of user credentials posted after a company is hit with a data breach where user data is compromised. These lists often expose emails, passwords, and usernames.
- Brute-Forcing, forcefully trying to guess what your credentials are using either manual or automated tools online.
- Social Engineering, using physiological methods to deceive a person from knowing the true intentions of the attacker. The attacker often is trying to extract data from the victim without being discovered.
We will explain the first two in more detail.